Ransomware attacks continue to disrupt businesses, hospitals, government agencies, and supply chains across the world. In 2025 alone, global ransomware incidents reached record highs as cybercriminal groups shifted toward data theft, double extortion, and AI-assisted phishing campaigns. These attacks now affect everything from healthcare scheduling systems to manufacturing operations and municipal services.
Organizations in the US face growing pressure from rising ransom demands, stricter compliance requirements, and longer operational downtime after attacks. Meanwhile, industries such as healthcare and manufacturing remain prime targets because even short disruptions can halt critical services and cause major financial losses. This article explores the latest ransomware attack statistics, including growth trends, industry impact, attack frequency, and emerging cybercrime patterns shaping the global threat landscape.
Editor’s Choice
- Global ransomware attacks increased by 32% in 2025, rising from 5,631 incidents in 2024 to 7,419 incidents in 2025.
- The US accounted for 50% of all ransomware incidents globally in 2025, making it the most targeted country worldwide.
- Manufacturing organizations represented 25% of global ransomware victims in 2025, the highest share among all industries.
- Healthcare organizations experienced 460 ransomware attacks and 182 data breaches during 2025, according to FBI reporting.
- Over 7,500 victim organizations appeared on ransomware leak sites in 2025, up nearly 58% year over year.
- The average ransom demand in 2025 reached $1.52 million, while the median ransom payment stood at $408,000.
- Ransomware-related cybercrime damages could exceed $265 billion annually by 2031, according to industry forecasts.
- Around 64% of ransomware victims refused to pay attackers in 2025 as organizations improved backup and recovery practices.
- The number of active ransomware groups climbed to 124 groups in 2025, including 73 newly formed operations.
Recent Developments
- Cybersecurity researchers reported that ransomware gangs increasingly shifted from encryption-based attacks to data exfiltration-only extortion during 2025.
- Data theft appeared in 74% of ransomware incidents in Q2 2025, overtaking traditional encryption tactics.
- AI-driven phishing and social engineering campaigns accelerated ransomware deployment in 2025, especially against large enterprises.
- The ransomware group Qilin emerged as one of the most active operators in 2025, alongside Akira and RansomHub.
- Cybersecurity analysts identified 34 new ransomware families during 2025, bringing the total known ransomware families to 425.
- In Q2 2025, the average ransomware payment rose to $1.13 million, more than doubling from the previous quarter.
- Healthcare ransomware demands dropped sharply in 2025, falling from $4 million in 2024 to about $343,000.
- The percentage of companies paying ransoms increased to 24.3% in 2025, compared to 14.4% in 2024.
- India recorded more than 265 million cyberattacks in 2025, reflecting rapid growth in regional cybercrime activity.
- Researchers found that 86% of ransomware attacks remain undisclosed publicly, showing the scale of hidden cyber incidents.
Global Ransomware Attack Overview
- Global ransomware incidents reached approximately 7,419 attacks in 2025, marking the highest annual total recorded so far.
- Cybercriminal groups posted more than 7,079 victims on dark web leak sites during 2025.
- The US remained the leading ransomware target, with over 3,671 reported attacks in one year.
- Manufacturing, healthcare, technology, and energy sectors accounted for nearly half of ransomware attacks targeting critical industries.
- Global ransomware attacks against critical sectors increased by 34% in 2025.
- Cybersecurity firms estimate that ransomware attacks now occur every 19 seconds worldwide.
- Professional services firms represented 20% of ransomware victims in Q2 2025, making them the most targeted business segment that quarter.
- Attackers increasingly targeted midsize companies, with firms employing 11,1,000 workers accounting for 64% of victims.
- Blockchain analysis estimated ransomware payments totaled around $820 million globally in 2025.
- Oil and gas ransomware incidents surged by 900% year over year in 2025.
Key Ransomware Attack Statistics (2024–2026)
- Global ransomware attacks increased from 5,631 incidents in 2024 to 7,419 incidents in 2025.
- Over 1,173 ransomware attacks were publicly confirmed by victims in 2025.
- The average ransomware demand reached $1.52 million in 2025.
- Median ransom payments declined from $150,000 in 2023 to $115,000 in 2024 as companies improved recovery planning.
- About 41% of organizations paid some form of ransom in 2025, down from 46% the prior year.
- Healthcare breaches affected more than 289 million individuals in 2024, driven largely by the Change Healthcare ransomware incident.
- The Change Healthcare ransomware attack exposed data from approximately 192.7 million individuals, making it one of the largest healthcare breaches ever recorded.
- In 2025, healthcare breach victims declined to roughly 62 million affected individuals, down sharply from 2024 levels.
- Organizations involving law enforcement during ransomware incidents reduced breach-related costs by nearly $1 million on average.
- Cybersecurity experts project ransomware-related global damages could exceed $265 billion annually by 2031.
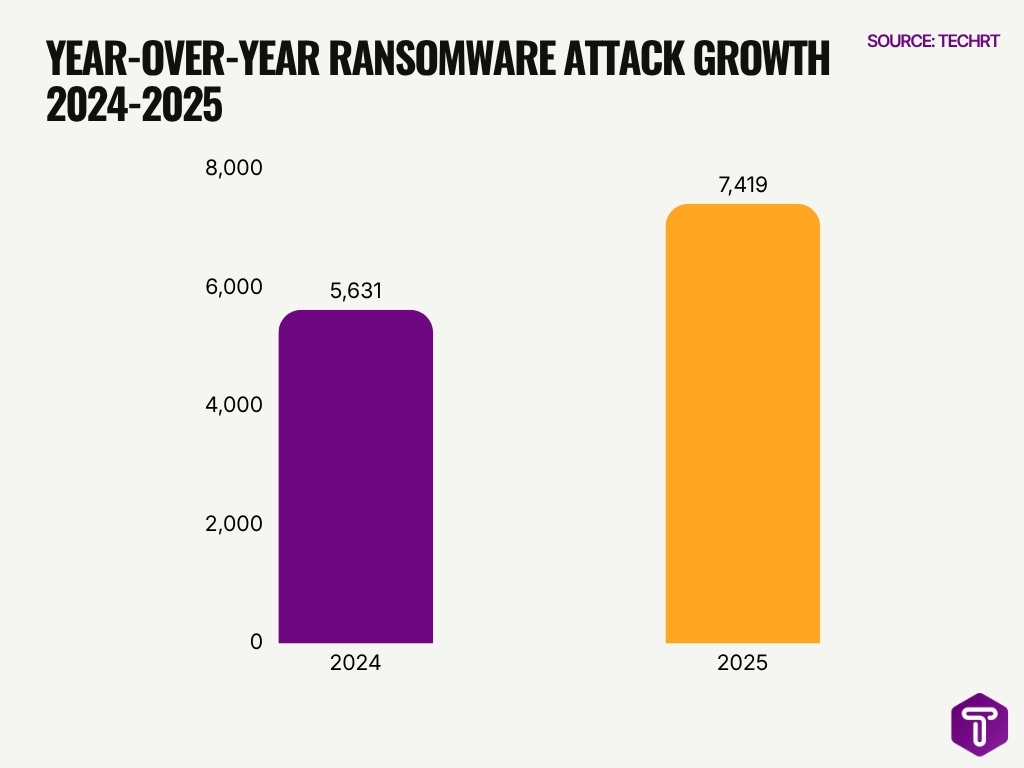
Year-over-Year Growth in Ransomware Attacks
- Ransomware incidents increased by 32% globally between 2024 and 2025.
- Public leak-site victim disclosures increased by 58% year over year in 2025.
- Undisclosed ransomware incidents rose by 37% during 2025, reflecting more hidden attacks.
- US ransomware attacks jumped by nearly 146% year over year, according to Zscaler ThreatLabz.
- Critical infrastructure ransomware attacks grew by 34% in 2025.
- The number of active ransomware groups expanded to 124 operations in 2025, marking an all-time high.
- Healthcare provider ransomware attacks in Australia rose by 83% in 2025 compared to 2024.
- Oil and gas sector ransomware incidents surged by 900% year over year in 2025.
- Ransomware-linked data exfiltration grew by 92% year over year, with attackers stealing 238 TB of data in 2025.
- Cybersecurity researchers observed that victim growth rates for ransomware attacks doubled during 2025.
Ransomware Attack Frequency and Volume by Year
- Cybersecurity researchers estimate that a ransomware attack occurs every 19 seconds worldwide in 2025.
- Global ransomware attack counts climbed from around 4,750 victims in 2024 to over 7,500 in 2025.
- More than 7,458 disclosed ransomware attacks were recorded globally during 2025.
- Healthcare organizations alone experienced 458 ransomware incidents in 2024.
- The FBI tracked 642 cyber events in the healthcare sector during 2025, including ransomware and data breaches.
- The top 10 ransomware groups collectively exfiltrated 238 terabytes of data during 2025 operations.
- RansomHub became one of the most active ransomware gangs with 833 known victims in 2025.
- Akira ransomware operators targeted at least 520 organizations globally in 2025.
- Clop ransomware accounted for approximately 488 victim organizations during 2025.
- Researchers identified 73 newly formed ransomware groups during 2025 alone.
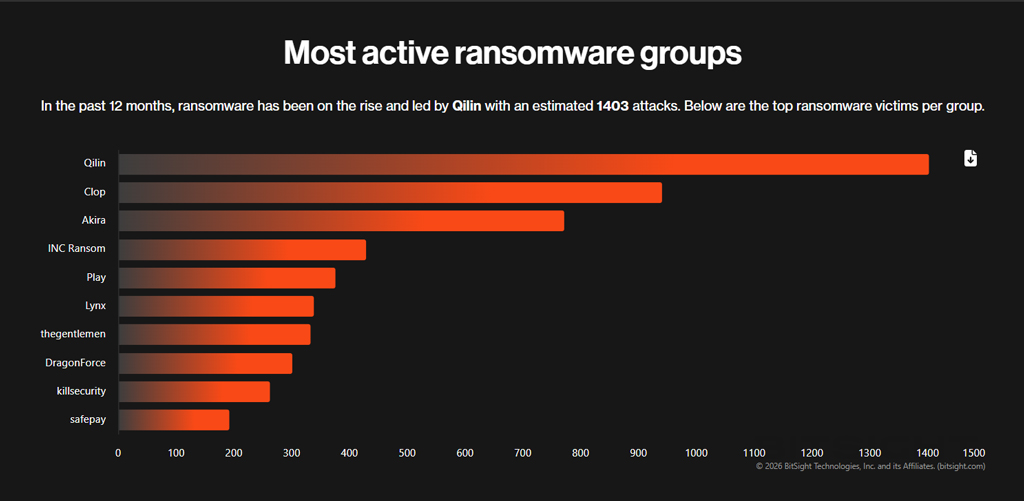
Most Active Ransomware Groups
- Qilin was the most active ransomware group, with an estimated 1,403 attacks in the past 12 months.
- Clop ranked second with 941 attacks, which is around 462 fewer attacks than Qilin.
- Akira was the third-most active group, recording 771 attacks during the same period.
- The top three ransomware groups, Qilin, Clop, and Akira, together accounted for 3,115 attacks.
- Qilin alone had more attacks than the combined total of INC Ransom, Play, Lynx, and the gentlemen, showing its dominant activity level.
- INC Ransom ranked fourth with 429 attacks, followed by Play with 375 attacks.
- Mid-tier ransomware groups such as Lynx, thegentlemen, and DragonForce recorded between 301 and 338 attacks each.
- killsecurity reported 262 attacks, placing it ninth among the most active ransomware groups.
- Safepay had the lowest count among the listed groups, with 192 attacks.
- The data shows a sharp gap between the top three groups and the rest, with Akira’s 771 attacks being nearly double INC Ransom’s 429 attacks.
Ransomware Attacks on Critical Infrastructure Sectors
- Critical infrastructure sectors accounted for nearly 50% of all ransomware incidents globally in 2025.
- Ransomware attacks targeting critical infrastructure increased by 34% year over year in 2025.
- The energy sector experienced a 900% surge in ransomware attacks during 2025.
- Water utility organizations in the US reported multiple ransomware intrusions tied to outdated industrial control systems.
- Transportation infrastructure attacks increased by 67% in 2025, affecting ports, rail systems, and logistics providers.
- Healthcare and public utilities remained among the top critical sectors listed on ransomware leak sites throughout 2025.
- The average downtime for critical infrastructure ransomware incidents reached 18 days in 2025.
- US federal agencies warned that ransomware groups are increasingly targeting operational technology systems rather than only IT networks.
- Industrial organizations paid some of the highest average ransom amounts, exceeding $2 million per incident in several cases.
- Nearly 75% of critical infrastructure organizations reported at least one ransomware-related disruption during the last 12 months.
Ransomware Attacks on Healthcare Organizations
- Healthcare organizations reported 460 ransomware attacks and 182 confirmed data breaches during 2025.
- The Change Healthcare ransomware incident exposed data from 192.7 million individuals, making it one of the largest healthcare breaches in US history.
- Healthcare ransomware attacks affected more than 289 million individuals in 2024.
- Average healthcare ransomware recovery costs reached $2.57 million in 2025.
- Around 67% of healthcare organizations experienced operational disruption after ransomware attacks in 2025.
- Healthcare organizations faced an average ransomware-related downtime of 11 days in 2025.
- The average healthcare ransom demand dropped from $4 million in 2024 to roughly $343,000 in 2025.
- About 53% of healthcare providers paid a ransom to restore operations or prevent data leaks during 2025.
- Electronic health record systems ranked among the most commonly targeted healthcare assets in ransomware campaigns.
- Third-party vendors and managed healthcare service providers became major ransomware entry points in 2025.
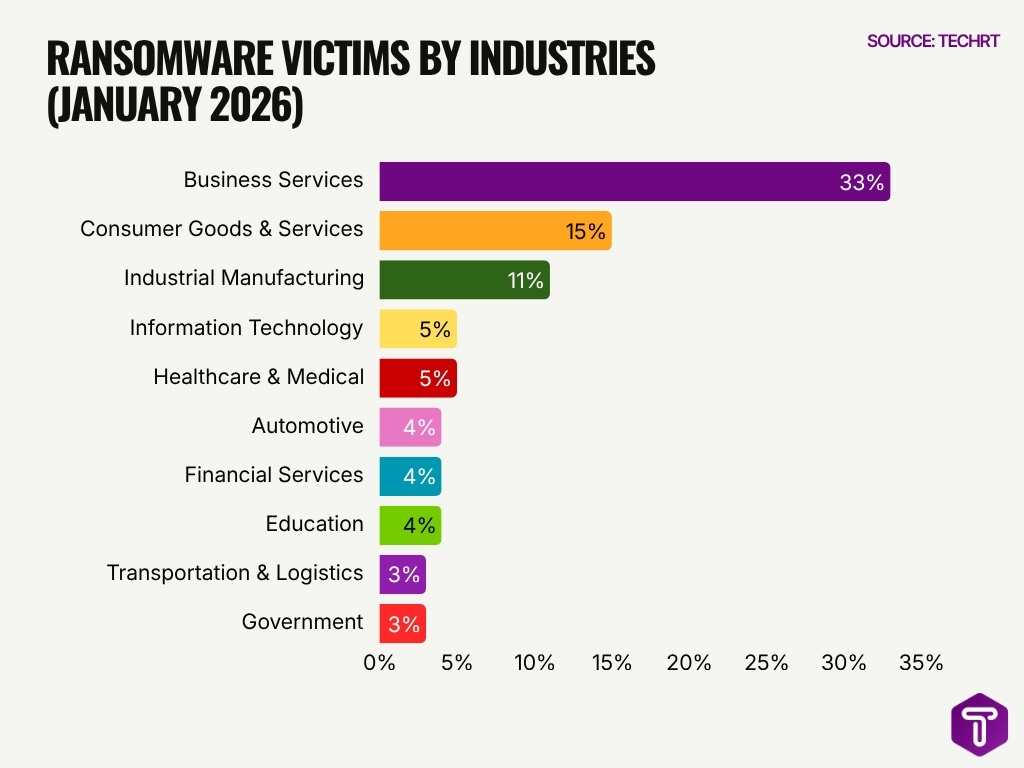
Ransomware Victims by Industry
- Business Services was the most affected industry, accounting for 33% of ransomware victims in January 2026.
- Consumer Goods & Services ranked second with 15%, showing strong attacker focus on customer-facing and service-driven businesses.
- Industrial Manufacturing was the third most targeted sector, representing 11% of ransomware victims.
- The top three industries, Business Services, Consumer Goods & Services, and Industrial Manufacturing, together made up 59% of reported ransomware victims.
- Information Technology and Healthcare & Medical each accounted for 5% of ransomware victims.
- Automotive, Financial Services, and Education recorded equal shares at 4% each.
- Transportation & Logistics and Government had the lowest shares among the listed sectors, each contributing 3%.
- The data suggests ransomware attacks were heavily concentrated in business-driven sectors, with Business Services alone accounting for nearly one-third of all victims.
- Industries with large digital operations, supply chains, customer data, and operational dependencies appear especially exposed to ransomware risk.
Ransomware Attacks on Government and Public Sector Entities
- Government agencies accounted for nearly 11% of global ransomware victims in 2025.
- US local governments saw a 22% increase in ransomware attacks targeting public records and emergency services.
- The average ransomware recovery cost for public-sector organizations exceeded $2.83 million in 2025.
- Around 59% of government entities reported service disruptions following ransomware attacks in 2025.
- Public-sector ransomware incidents caused an average downtime of 10.8 days globally.
- Nearly 68% of US school districts and municipalities were targeted due to aging IT infrastructure vulnerabilities.
- More than 2,700 state and local government organizations worldwide faced ransomware disruptions in 2025.
- Election infrastructure attacks rose by 18%, targeting voter databases and systems ahead of elections.
- Approximately 38% of government organizations paid ransom demands during 2025 incidents.
- Public transportation systems in 15+ US cities reported ransomware-related operational disruptions in 2025.
Ransomware Attacks on Manufacturing and Industrial Organizations
- Manufacturing represented 25% of global ransomware victims in 2025, the largest share among all industries.
- Industrial ransomware attacks increased by 41% year over year between 2024 and 2025.
- Operational technology systems became a primary target in manufacturing ransomware incidents during 2025.
- Average downtime for manufacturing ransomware attacks reached 22 days in 2025.
- Around 71% of manufacturing companies reported revenue losses after ransomware-related production outages.
- Supply chain disruption became a major secondary impact of manufacturing ransomware incidents in North America and Europe.
- Industrial firms faced average ransom demands exceeding $1.9 million in 2025.
- Automotive manufacturers experienced increased targeting from ransomware gangs exploiting third-party supplier access.
- Nearly 60% of manufacturing organizations restored operations using backups instead of paying ransom demands in 2025.
- Asia-Pacific manufacturing hubs recorded some of the fastest ransomware growth rates globally during 2025.
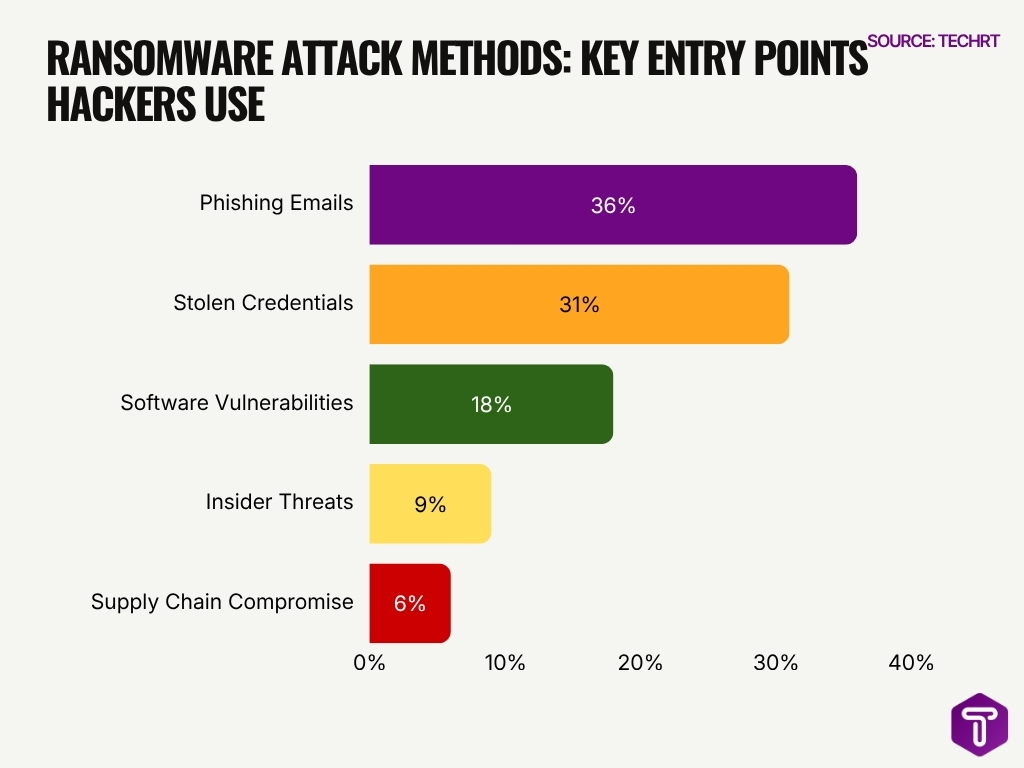
Ransomware Attack Methods
- Phishing emails are the leading ransomware attack method, accounting for 36% of attacks.
- Stolen credentials are the second-largest attack vector, responsible for 31% of ransomware incidents.
- Together, phishing emails and stolen credentials make up 67% of ransomware attack methods, showing that identity and email-based threats remain the biggest risks.
- Software vulnerabilities contribute to 18% of ransomware attacks, highlighting the importance of regular patching and vulnerability management.
- Insider threats account for 9% of ransomware attack methods, showing that internal security risks cannot be ignored.
- Supply chain compromise represents 6% of ransomware attacks, making it the smallest category in this dataset.
- The data shows that ransomware attackers mainly rely on human error, weak credentials, and unpatched systems to gain access.
- Organizations can reduce ransomware risk by focusing on email security, credential protection, multi-factor authentication, and timely software updates.
Ransomware Attacks on Small and Medium-Sized Businesses
- Small and medium-sized businesses accounted for approximately 43% of ransomware victims globally in 2025.
- SMB ransomware attacks increased by 28% year over year between 2024 and 2025.
- Businesses with fewer than 1,000 employees represented 64% of ransomware victims in Q2 2025.
- The average ransomware recovery cost for SMBs exceeded $1.5 million in 2025.
- Around 47% of SMBs reported paying ransom demands during 2025 incidents.
- SMBs experienced average ransomware downtime of 7 to 14 days, depending on industry and backup readiness.
- Email phishing remained the leading ransomware entry vector for small businesses in 2025.
- About 75% of SMBs lacked a fully tested incident response plan in 2025.
- Managed service providers became increasingly targeted because attackers could pivot into multiple SMB networks simultaneously.
- Nearly one-third of SMB ransomware victims reported permanent customer loss after major incidents.
Ransomware-as-a-Service (RaaS) Ecosystem Statistics
- The number of active ransomware groups reached 124 operations globally in 2025, an all-time high.
- Researchers identified 73 newly formed ransomware groups during 2025 alone.
- RansomHub emerged as one of the most active RaaS groups, claiming 833 victims during 2025.
- Akira ransomware operators targeted at least 520 organizations globally in 2025.
- Clop ransomware accounted for nearly 488 disclosed victims during 2025 campaigns.
- RaaS operators commonly shared profits with affiliates through commission models ranging from 20% to 30% of collected ransom payments.
- Cryptocurrency laundering services played a major role in ransomware monetization ecosystems.
- Dark web marketplaces increasingly offered ransomware kits bundled with phishing templates and credential-stealing tools.
- AI-assisted malware customization accelerated the speed at which ransomware affiliates launched campaigns in 2025.
- Law enforcement takedowns disrupted several major ransomware gangs during 2025, but smaller affiliate networks quickly replaced them.
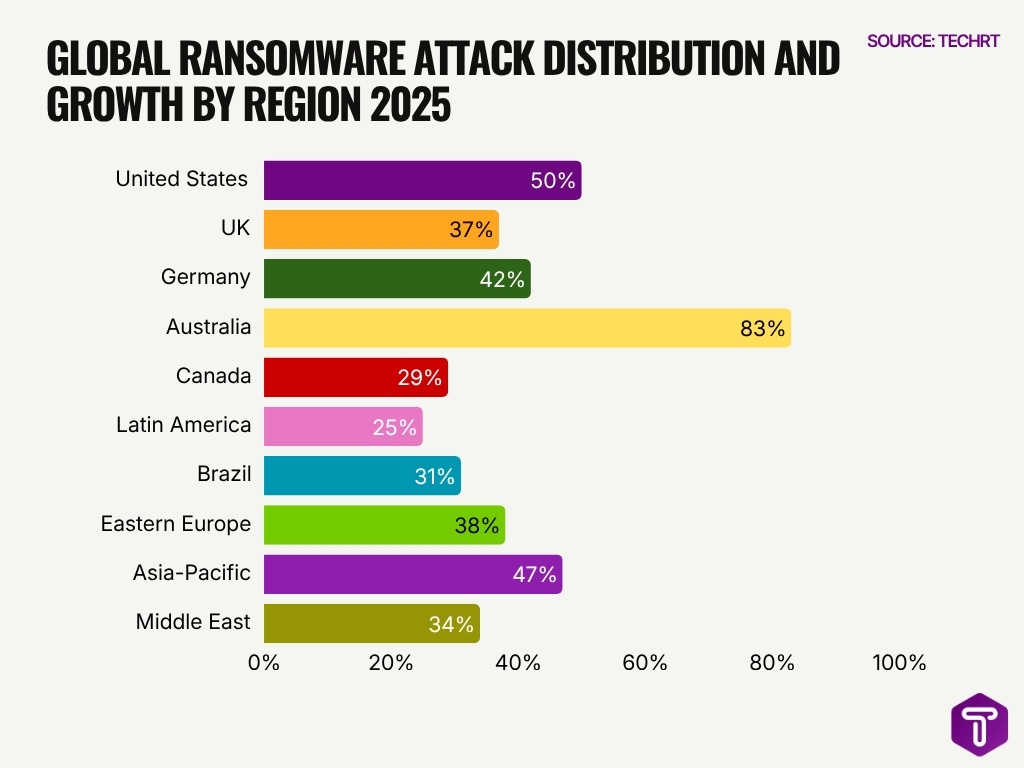
Ransomware Attack Rates by Region and Country
- The United States accounted for roughly 50% of global ransomware incidents during 2025.
- The UK ranked among Europe’s most targeted countries for ransomware attacks in 2025, with attacks up 37%.
- Germany reported a 42% rise in ransomware attacks targeting manufacturing and automotive sectors during 2025.
- India recorded more than 265 million cyberattack events in 2025, including ransomware and malware campaigns.
- Australia experienced an 83% increase in healthcare ransomware incidents during 2025.
- Canada reported rising ransomware attacks against municipalities, healthcare systems, and universities in 2025, up 29%.
- Latin American countries saw ransomware growth rates exceed 25% year over year in 2025, with Brazil leading at 31%.
- Eastern European ransomware groups remained responsible for 38% of global ransomware activity during 2025.
- Asia-Pacific organizations faced a 47% increase in supply chain ransomware attacks targeting manufacturing ecosystems in 2025.
- Middle Eastern energy and infrastructure organizations experienced a 34% rise in ransomware targeting throughout 2025.
Ransomware Attack Downtime and Business Disruption
- The average ransomware-related downtime across industries reached 21 days in 2025.
- Manufacturing organizations experienced average operational outages lasting 22 days after ransomware attacks.
- Healthcare providers reported an average downtime of 11 days following ransomware incidents in 2025.
- Around 67% of ransomware victims experienced significant revenue disruption due to prolonged recovery periods.
- Small businesses lost an average of $98,000 per ransomware incident when accounting for downtime and recovery expenses.
- Nearly 47% of organizations reported customer churn after publicly disclosed ransomware incidents.
- Transportation and logistics companies reported supply chain interruptions averaging 6.4 days during ransomware recovery.
- Public-sector organizations experienced service disruptions affecting emergency response systems, online portals, and payment processing operations.
- Organizations with tested incident response plans reduced downtime by nearly 50% compared to unprepared organizations.
- More than 70% of ransomware victims reported operational disruption extending beyond IT systems into customer-facing services.
Ransomware Demand Amounts and Payment Rates
- The average ransomware demand reached approximately $1.52 million in 2025.
- Median ransomware payments stood at roughly $408,000 during 2025 incidents.
- Around 41% of ransomware victims paid attackers in some form during 2025.
- Organizations that paid ransoms still spent substantial amounts on recovery, averaging $2.73 million in total remediation costs.
- Healthcare organizations saw ransom demands decline sharply from $4 million in 2024 to approximately $343,000 in 2025.
- Cryptocurrency remained the dominant ransomware payment method, accounting for over 98% of ransom transactions globally.
- Roughly 64% of organizations refused to pay ransom demands in 2025 because of improved backup strategies and regulatory concerns.
- Law enforcement intervention reduced ransomware-related costs by nearly $1 million on average for affected organizations.
- Double-extortion attacks pushed ransom demands significantly higher because attackers threatened to leak stolen data publicly.
- Several ransomware groups offered installment-style payment negotiations during 2025 to increase collection rates from victims.
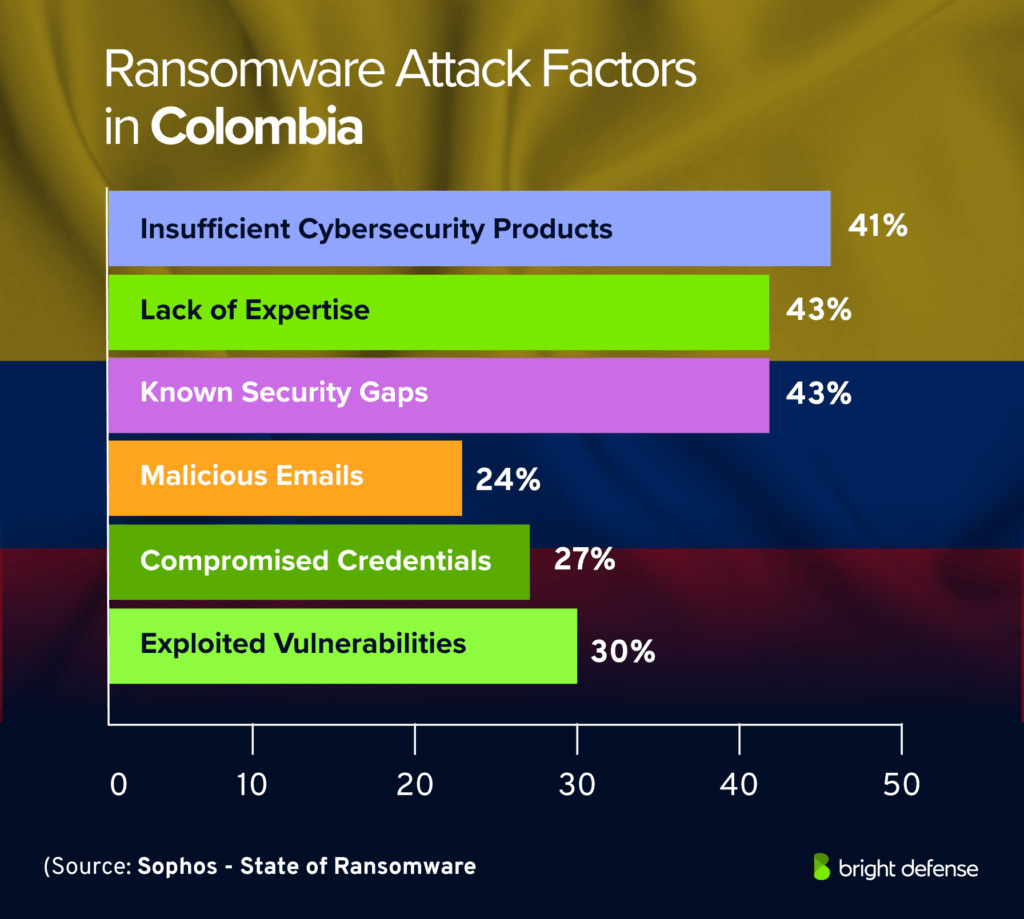
Ransomware Attack Factors in Colombia
- Lack of expertise and known security gaps are the leading ransomware attack factors in Colombia, each accounting for 43%.
- Insufficient cybersecurity products closely follow at 41%, showing that many organizations may lack adequate security tools or protection systems.
- Exploited vulnerabilities contribute to 30% of ransomware attack factors, highlighting the importance of regular software updates and patch management.
- Compromised credentials account for 27%, suggesting that weak passwords, stolen logins, and poor access controls remain major security risks.
- Malicious emails represent 24%, indicating that phishing and email-based attacks continue to be an important ransomware entry point.
- The top three factors, lack of expertise, known security gaps, and insufficient cybersecurity products, all exceed 40%, showing that internal security readiness is a major ransomware challenge in Colombia.
Data Exfiltration and Double-Extortion Ransomware Statistics
- Data theft appeared in 74% of ransomware incidents during Q2 2025, surpassing traditional encryption-only attacks.
- Cybercriminals exfiltrated approximately 238 terabytes of victim data during ransomware operations in 2025.
- Double-extortion tactics became standard practice for most major ransomware groups by 2025.
- Around 86% of ransomware attacks involving data theft were never publicly disclosed.
- Ransomware leak sites published more than 7,000 victim organizations during 2025.
- Legal, healthcare, and financial services organizations faced some of the highest data exfiltration risks because of sensitive records exposure.
- The average cost of a data breach involving ransomware reached $5.13 million globally in 2025.
- Threat actors increasingly use stolen data to pressure victims through public leak websites and direct customer notifications.
- Researchers identified a growing trend toward “exfiltration-only ransomware,” where attackers skipped file encryption entirely.
- Cloud storage repositories became common targets for ransomware-linked data theft campaigns in 2025.
Future Ransomware Attack Trends and Predictions
- Ransomware damages could reach $265 billion annually by 2031, according to Cybersecurity Ventures.
- AI-powered phishing and automated reconnaissance are expected to make ransomware campaigns faster, with some 2026 forecasts citing 10,000 personalized phishing emails per second.
- Critical infrastructure remains a high-value target, and one 2026 report said the U.S. accounted for over 55% of observed victims in a ransomware study.
- Exfiltration-only and extortionware attacks are rising, with threat reports describing a shift away from encryption-only tactics toward data theft and leak pressure.
- Cloud ransomware is growing in 2026, with attackers targeting identity, APIs, SaaS integrations, and cloud backups instead of just endpoints.
- Zero Trust can help reduce ransomware risk by enforcing continuous verification, MFA, and least privilege across enterprise environments.
- Governments are moving toward stricter ransomware reporting rules, including Australia’s 72-hour disclosure requirement and the U.S. 24-hour ransom payment reporting for covered entities.
- Small businesses are becoming easier targets, with one 2026 report saying attacks on SMBs rose 68% in 2025 and average demands hit $247,000.
- Cyber insurers are tightening requirements, now often demanding MFA everywhere and immutable or offline backups before coverage is granted.
- Ransomware groups are fragmenting into smaller RaaS affiliate ecosystems, with specialized actors separating access, intrusion, and extortion work.
Frequently Asked Questions (FAQs)
How many ransomware attacks were reported globally in 2025?
Global ransomware attacks reached approximately 7,419 incidents in 2025, reflecting a 32% increase from 2024.
What was the average ransomware demand in 2025?
The average ransomware demand in 2025 climbed to $1.52 million, while the median ransom payment reached $408,000.
Which country faced the highest share of ransomware attacks in 2025?
The United States accounted for around 50% of global ransomware incidents in 2025, with more than 3,671 reported attacks.
What percentage of organizations experienced ransomware attacks in the past year?
According to CrowdStrike’s 2025 ransomware survey, 78% of organizations reported experiencing a ransomware attack within the previous 12 months.
How much could ransomware damage cost globally by 2031?
Cybersecurity researchers project ransomware-related damages could exceed $265 billion annually by 2031, with attacks expected to occur every two seconds.
Conclusion
Ransomware attacks continued to evolve rapidly, with cybercriminal groups adopting more advanced tactics, larger extortion demands, and increasingly targeted attacks against critical sectors. Manufacturing, healthcare, government, and small businesses remained among the most affected industries because operational disruptions in these sectors create immediate financial pressure.
The data also shows a growing shift toward double-extortion and data theft-focused campaigns, while AI-assisted phishing and ransomware-as-a-service models lowered the barrier for cybercriminal activity. At the same time, organizations improved resilience through stronger backups, multifactor authentication, incident response planning, and zero-trust security frameworks.
As ransomware activity expands globally, businesses and public-sector organizations will likely continue increasing cybersecurity investments to reduce downtime, protect sensitive data, and meet evolving compliance requirements. The statistics throughout this report highlight how ransomware has become both a cybersecurity challenge and a major operational risk across nearly every industry.


Leave a comment
Have something to say about this article? Add your comment and start the discussion.